Topic 1: Exam Pool A
Which system consists of a publicly available set of databases that contain domain name
registration contact information?
A.
WHOIS
B.
CAPTCHA
C.
IANA
D.
IETF
WHOIS
What is the proper response for a NULL scan if the port is closed?
A.
SYN
B.
ACK
C.
FIN
D.
PSH
E.
RST
F.
No response
RST
Shellshock allowed an unauthorized user to gain access to a server. It affected many
Internet-facing services, which OS did it not directly affect?
A.
Linux
B.
Unix
C.
OS X
D.
Windows
Windows
Which of the following is a command line packet analyzer similar to GUI-based Wireshark?
A.
nessus
B.
tcpdump
C.
ethereal
D.
jack the ripper
tcpdump
Tcpdump is a data-network packet analyzer computer program that runs under a command-line interface. It allows the user to display TCP/IP and other packets being
transmitted or received over a network to which the computer is attached. Distributed under
the BSD license, tcpdump is free software.
https://www.wireshark.org/
Wireshark is a free and open-source packet analyzer. It is used for network
troubleshooting, analysis, software and communications protocol development, and
education.
NOTE: Wireshark is very similar to tcpdump, but has a graphical front-end, plus some
integrated sorting and filtering options.
Which regulation defines security and privacy controls for Federal information systems and
organizations?
A.
HIPAA
B.
EU Safe Harbor
C.
PCI-DSS
D.
NIST-800-53
NIST-800-53
Explanation:
NIST Special Publication 800-53 provides a catalog of security and privacy controls for all
U.S. federal information systems except those related to national security. It is published by
the National Institute of Standards and Technology, which is a non-regulatory agency of the
United States Department of Commerce. NIST develops and issues standards, guidelines,
and other publications to assist federal agencies in implementing the Federal Information
Security Modernization Act of 2014 (FISMA) and to help with managing cost-effective
programs to protect their information and information systems.
An attacker, using a rogue wireless AP, performed an MITM attack and injected an HTML code to embed a malicious applet in all HTTP connections.
When users accessed any page, the applet ran and exploited many machines. Which one
of the following tools the hacker probably used to inject HTML code?
A.
Wireshark
B.
Ettercap
C.
Aircrack-ng
D.
Tcpdump
Ettercap
You have successfully comprised a server having an IP address of 10.10.0.5. You would
like to enumerate all machines in the same network quickly.
What is the best Nmap command you will use?
A.
nmap -T4 -q 10.10.0.0/24
B.
nmap -T4 -F 10.10.0.0/24
C.
nmap -T4 -r 10.10.1.0/24
D.
nmap -T4 -O 10.10.0.0/24
nmap -T4 -F 10.10.0.0/24
Explanation: https://nmap.org/book/man-port-specification.html
NOTE: In my opinion, this is an absolutely wrong statement of the question. But you may
come across a question with a similar wording on the exam. What does "fast" mean? If we
want to increase the speed and intensity of the scan we can select the mode using the -T
flag (0/1/2/3/4/5). At high -T values, we will sacrifice stealth and gain speed, but we will not
limit functionality.
«nmap -T4 -F 10.10.0.0/24» This option is "correct" because of the -F flag.
-F (Fast (limited port) scan)
Specifies that you wish to scan fewer ports than the default. Normally Nmap scans the
most common 1,000 ports for each scanned protocol. With -F, this is reduced to 100.
Technically, scanning will be faster, but just because we have reduced the number of ports
by 10 times, we are just doing 10 times less work, not faster.
Peter extracts the SIDs list from Windows 2000 Server machine using the hacking tool
"SIDExtractor". Here is the output of the SIDs:
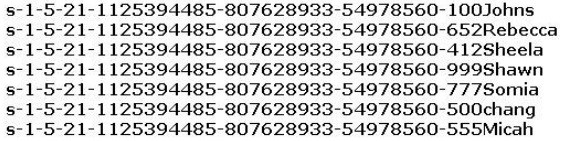
From the above list identify the user account with System Administrator privileges.
A.
John
B.
Rebecca
C.
Sheela
D.
Shawn
E.
Somia
F.
Chang
G.
Micah
Chang
A new wireless client is configured to join a 802.11 network. This client uses the same
hardware and software as many of the other clients on the network. The client can see the
network, but cannot connect. A wireless packet sniffer shows that the Wireless Access
Point (WAP) is not responding to the association requests being sent by the wireless client.
What is a possible source of this problem?
A.
The WAP does not recognize the client’s MAC address
B.
The client cannot see the SSID of the wireless network
C.
Client is configured for the wrong channel
D.
The wireless client is not configured to use DHCP
The WAP does not recognize the client’s MAC address
Explanation: https://en.wikipedia.org/wiki/MAC_filtering
MAC filtering is a security method based on access control. Each address is assigned a
48-bit address, which is used to determine whether we can access a network or not. It
helps in listing a set of allowed devices that you need on your Wi-Fi and the list of denied
devices that you don’t want on your Wi-Fi. It helps in preventing unwanted access to the
network. In a way, we can blacklist or white list certain computers based on their MAC
address. We can configure the filter to allow connection only to those devices included in
the white list. White lists provide greater security than blacklists because the router grants
access only to selected devices.
It is used on enterprise wireless networks having multiple access points to prevent clients
from communicating with each other. The access point can be configured only to allow
clients to talk to the default gateway, but not other wireless clients. It increases the
efficiency of access to a network.
The router allows configuring a list of allowed MAC addresses in its web interface, allowing
you to choose which devices can connect to your network. The router has several functions
designed to improve the network's security, but not all are useful. Media access control
may seem advantageous, but there are certain flaws.
On a wireless network, the device with the proper credentials such as SSID and password
can authenticate with the router and join the network, which gets an IP address and access
to the internet and any shared resources.
MAC address filtering adds an extra layer of security that checks the device’s MAC address
against a list of agreed addresses. If the client’s address matches one on the router’s list,
access is granted; otherwise, it doesn’t join the network.
Why would you consider sending an email to an address that you know does not exist
within the company you are performing a Penetration Test for?
A.
To determine who is the holder of the root account
B.
To perform a DoS
C.
To create needless SPAM
D.
To illicit a response back that will reveal information about email servers and how they
treat undeliverable mail
E.
To test for virus protection
To illicit a response back that will reveal information about email servers and how they
treat undeliverable mail
| Page 5 out of 57 Pages |
| Previous |